ChangeLog
(Last update: 02/05/20)MOXiI is now self-published, which enables me to keep the book continuously updated! Unlike a traditional print book, with which you have to wait for a new edition, I can update the original HTML file, reprint to PDF, and submit another batch to print! This will obviously not help copies already printed at that point, but any future copies going to print will automatically be as up-to-date as possible. This means that whenever one chooses to buy the book, he or she is guaranteed the latest and greatest edition. Think of it as you would of software - wherein new versions come out every so often.
Over time, this will inevitably open up quite a gap between any past-printed versions and the latest ones. Beginning with v1.0.1, I started this changelog to help people track "What's New". If you bought an older copy and, at some point, wish to re-purchase the latest version of the book, please drop me a note and inform me you already have a previous version. I would be happy cut you a $15/0.05BTC discount when you get a new copy. Note that you have to use BTC or Paypal for that - I can't do that via Amazon, sorry. (And, hey - when's the last time a publisher offered you such a discount on upgrade, or even made an effort to keep a book so up-to-date?)
Volume I: Volume II Volume III
| Date | Version | Notes | ||||||
|---|---|---|---|---|---|---|---|---|
| 02/06/2018 | 1.0.2 | |||||||
| 03/06/2018 | 1.0.3 | |||||||
| 05/01/2018 | 1.0.4 | SEND_ONCE rights ARE transitive - not clonable, but movable. Table 11-1 should therefore read MOVE only for SEND ONCE. (And yes, I'm paying 0.01BTC for this - it was well deserved). proc_info's private PROC_PIDUNIQIDENTIFIERINFO flavor (#17)."
|
||||||
| 9/21/18 | v1.1 (really should have been v.1.0.6..) | Minor improvements for Darwin 18. Nothing finalized yet. So far, we have:
[get/set]wgroups to Table 8-8, even though they're unimplemented, in an attempt to reach 100% syscall coverage through the trilogytlv_atexit() (from <mach-o/dyld.h>) for Thread Local destructors | ||||||
| 12/10/2018 | v1.2 | One year later, a major update, with over 60 (+12%) densely packed pages! Brings back some stuff I had originally pushed to Volume II now that Volume II is close to finish and I know how to divide the material better. This includes:
I had originally thought I'd include that in Volume II, but now that Volume II is being finalized I realized its own networking chapter (from the kernel perspective) is already quite big - and user mode really belongs in Volume I.. struct fileproc, filedesc, filEglob and all that fun stuff) in Volume II, but the syscalls certainly make more sense in I. iopolicysys (#proc_rlimit_control (#446) and process_policy (#323)malloc_replay tool
| ||||||
| 3/17/2019 | v1.2.1 | Minor additions:
| ||||||
| 06/17/2019 | v1.3 | 
|
||||||
| 07/29/19 08/20/19 | v1.3-1 (19β4,6) | COMPRESSION_LZFSE (type 7) in DMGspid_shutdown_sockets() is on target pid, and mentioned assertiond calls it when device sleepsinit_featureflags run on startupxattr_name_with_flags(3) (Thanks, @Howardnoakley!)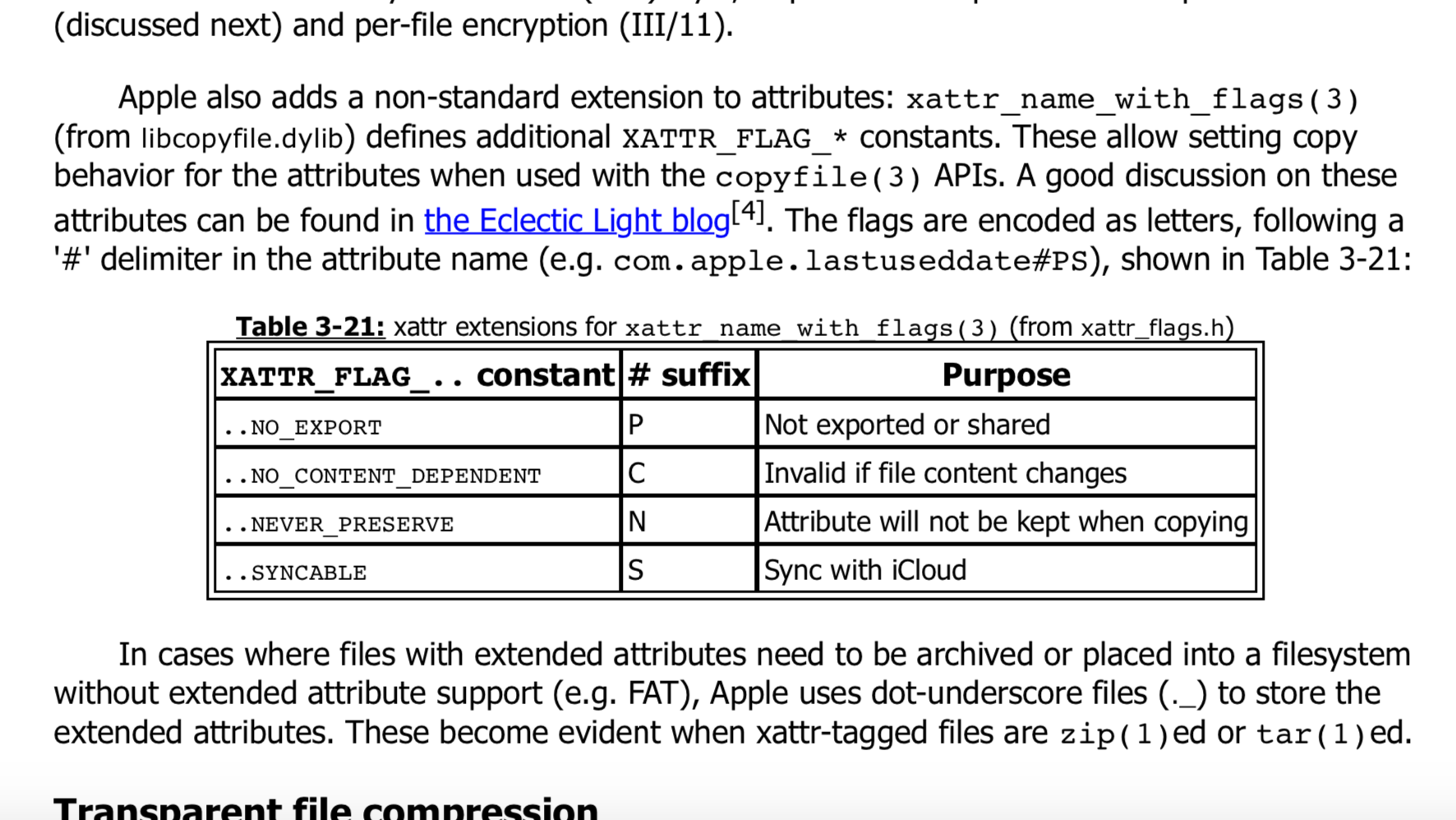
| ||||||
| 09/22/2019 | v.1.3.3.7 | 
watchevent/waitevent/modwatch syscalls as file descriptor based alternative to fseventsinitgroups() (#243) and settid_with_pid() (#311 :-) to Table 8-8psynch and pthread syscalls, as well as proprietary ulock_[wait/wake]()
terminate_with_payload() and os_fault_with_payload() (#520, 529) after abort_with_payload() (#521) in Ch15. Pedantic, I agree, but 100% syscall coverage doesn't come easy.. | ||||||
| v.1.3.3.7.7.1 | ? |
|
Volume I Volume II Volume III
| Date | Version | Notes |
|---|---|---|
| 11/3/2019 | 1.0.1 | ipc_kobject_alloc_port mentioned as new way (from Darwin 19) to alloc ports for kobjects |
| 02/02/2020 | 1.0.2 |
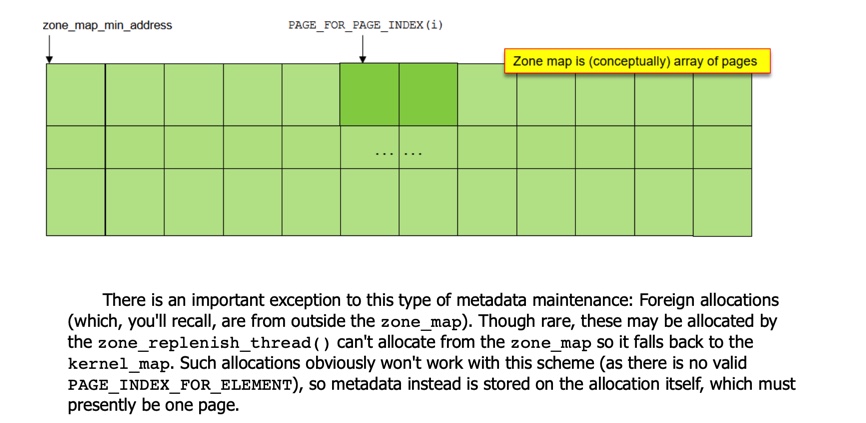
zone_require():
and, although in a footnote, Brandon gets the only resource reference in Chapter 12 :-)
|
Volume I Volume II Volume III
| Date | Version | Notes |
|---|---|---|
| 10/17/2016 | 1.0 | |
| 11/04/2016 | 1.0.1 | |
| 11/16/2016 | 1.1 | |
| 01/10/2017 | 1.2 | |
| 02/04/2017 | 1.3g | |
| 03/21/2017 | 1.3.1 | |
| 08/07/2017 | 1.4 |
|
09/28/2017 One year later :-) | 1.4.2 |
CS_OPS_CLEARINSTALLER in Table 5-28 |
| 12/01/2017 | 1.4.3 |
|
| 12/31/2017 | 1.5 |
|
| 03/15/2018 | 1.5.1 | sbtool, after Table 8-23. |
| 05/01/2018 | 1.5.2 | CS_EXECSEG.. flags in code signature 0x20400 (still apparently unused) |
| 06/25/2018 | 1.6 | |
| 08/28/2018 | 1.6.1 | "Apple has extended audit sessions to be carried over Mach ports and added proprietary system calls in Darwin 10. The |
| 09/24/2018 | 1.6.2 | iOS 12 changes (in Appendix B of 1.6) finalized, TCC version 13, Sandbox 865 hook count actually reduced by one or two, ARMv8.3 PAC security impact discussed |
| 1.6.4 (03/15/2019) | 1.6.4 | Minor updates:
CS_OPS_CLEARINSTALLER (Darwin 17) and CS_TEAMID (Darwin 18) to Table 5-28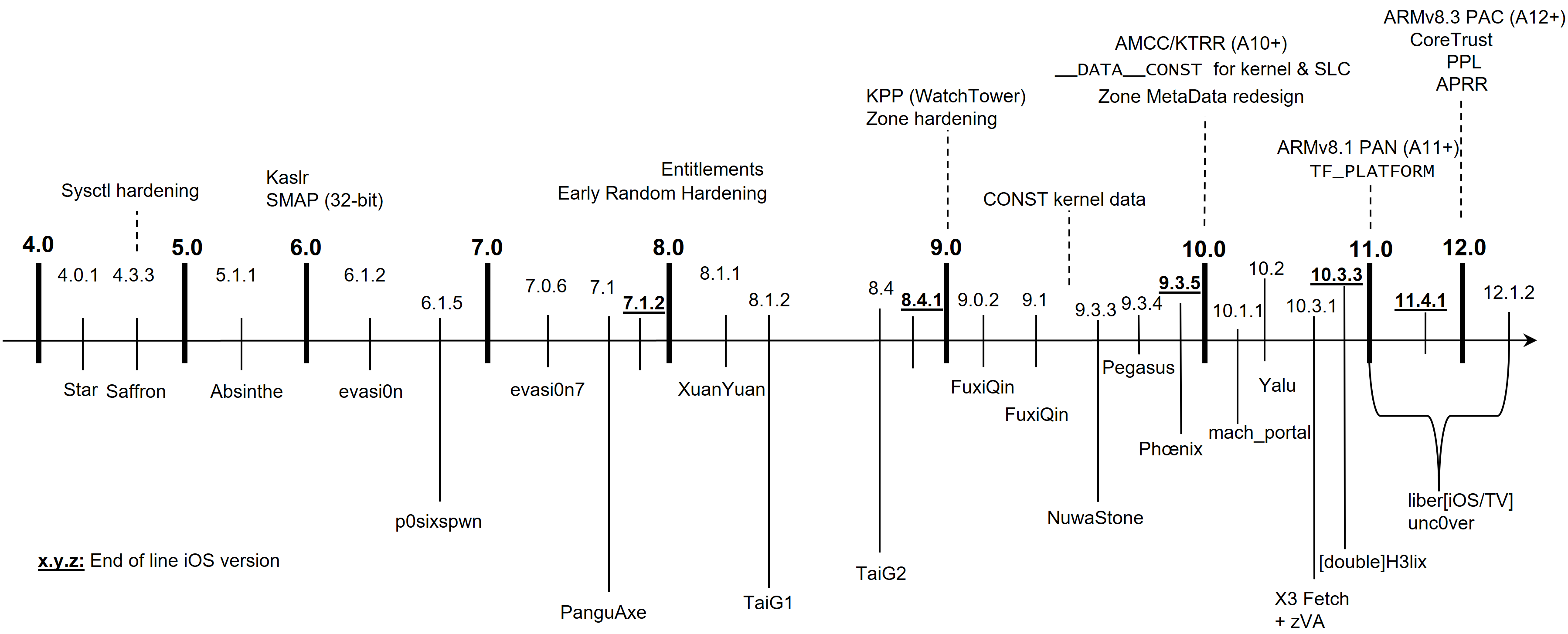
PROTECTION_CLASS_F appears deprecated as of Darwin 16 (_E was never used)OSUnserializeBinary, not OSUnserializeXML (though the latter calls the former anyway) |
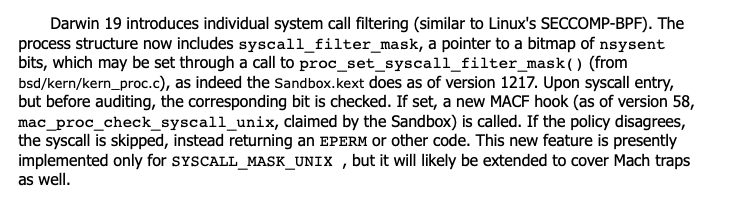
| 1.6.6n | 02/10/2020 | mac_syscall supportmac_proc_check_unix_syscall |
The book is now about
Updates
- 03/15/2019 - Figure 5-4: Code signatures have since been updated - and the new format (0x20500) is shown below:
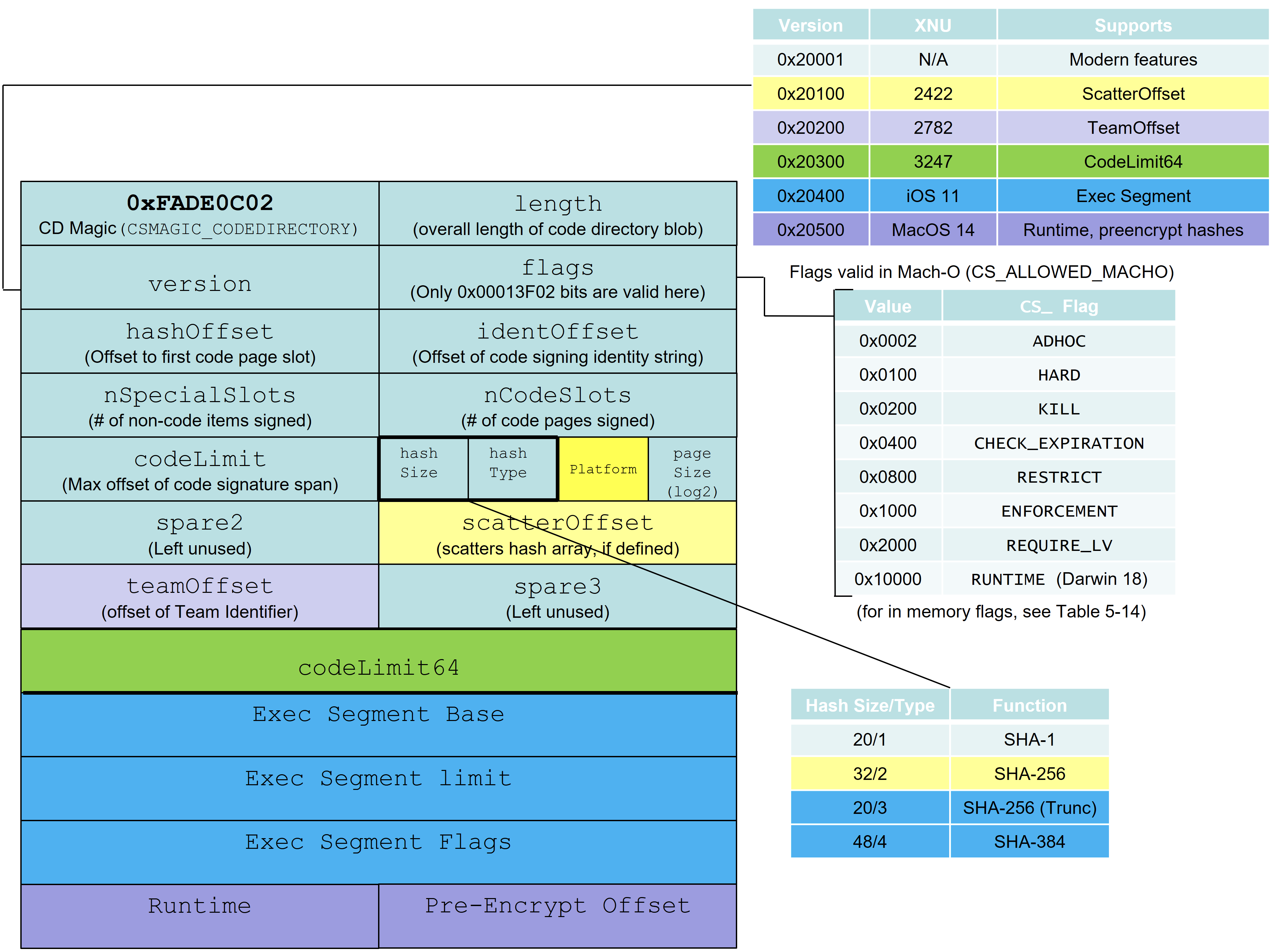
- Also updated Table 10-2 to account for new
kTCCService*constants:

-
09/19/19 - Darwin 19 bumps this even further with 30+ more services - 22 alone for
kTCCServiceSensorKit*, 3 forSystemPolicy[Desktop/Downloads/Documents]Folder,ScreenCapture,FileProvider[Presence/Domain],Contacts[Full/Limited],Bluetooth[WhileInUse/Always],ListenEvent, and possibly a few others I missed.. - 10/17/2017 - DMG signatures: Whilst covering DMGs in Volume I (out next week!) I realized I omitted that as of somewhere in 10.11.x DMGs can be signed with embedded, not just detached signatures. This adds special slot -6, and hashes the entire DMG (sans koly and, obviously, signature) as the single slot 0 of the signature. This will be put into v1.4.3 and later.
Errata
- Table 8-19:
distributed-notification-postis, of course, to post to Distributed Notification Center, not Darwin - Chapter 22.5, discussion of
mach_ports_register: The explanation should make it clear the bug is in the kernel-side MIG generated code. Readers might get the impression the bug is in Listing 22a-7. A better explanation (put into versions after 1.4 and the PhJB PDF) would be:The call to this code is automatically generated by the Mach Interface Generator (MIG, q.v. I/11), which takes care (in user-mode) of properly initializing the portsCnt variable so that it matches the length of the OOL ports descriptor sent in the message. But user-mode MIG can easily be bypassed, and its code tweaked to deliberately mismatch the two values. The sanity checks restrict the value of portsCnt to be between 1 and 3 - but the kernel-side MIG checks fail to validate that it actually matches the number of ports in the ool descriptor itself. This still allows for an out of bounds condition, wherein extra port elements in kernel memory can be read - and then dereferenced - leading to a Use After Free (UaF) bug.
- Chapter 25 - The QiLin Toolkit - Page 486 - "and in particular the task_for_pid/com.apple.system-task-ports" - mistakenly inserted as the result of a vi '.' operation. Should just be ignored (considering that this specific entitlement pair is held by
sysdiagnoseandps, as shown already at the top of the same page, before the listing).
FAQ
A: see per above. With the Pangu Chapter, I made that public, and a lot of Volume III's extra chapters are free (hyperlinked, above). BUT - I can't do that for every chapter. Again, I MUST apologize for not being able to concoct some "update" scheme wherein I nickel and dime for so and so extra pages. But I can't do that because (A) it would be nickel and diming and (B) I can't track already 500 copies in first month or so. Before you get riled by this, pause for a sec and realize that you wouldn't expect that from any "traditional" print book, which grows obsolete as soon as it sees print.
 .
.