SUpraudit - An actually useful praudit(1) for MacOS
What is this?
You may or may not be familiar with BSM auditing. A legacy of the dearly departed Solaris OS, which lives on in FreeBSD, Linux and - of course - MacOS. Auditing is detailed in my *OS Internals::Security & Insecurity's Chapter 2, and is one of the diamonds in the rough as far as system monitoring is concerned. Though not as powerful as the MAC Framework (and unable to proact, only react to operations), no other framework combines the ease of live monitoring with the advantages of pure user mode. The kernel is still very much involved - but you neither can nor should modify its auditing logic, which is enabled by default.
Apple took the set of default Solaris tools (namely, grep(1) friendly even when used with -l (single line output). And its XML output (-x) isn't that shabby either.
Enter: SUpraudit
After 25 or so years(?) it's time for a revamp. I've reversed
root@Zephr (~) # supraudit -h
supraudit: illegal option -- -h
usage: supraudit [-lnpx] [-r | -s] [-d del] [file ...]
OR
supraudit [-S [-C] |-J] [-F filter] [-O output]
-S: SuperAudit records (much more readable)
-C: Color (because everything looks better in color)
-J: JSON
-L: Relay to local syslog
-F: Filter by predefined rules - files, net, proc
-O: Log to specified outputfile
This is J's supraudit, compiled on May 22 2018.
Latest version always free @http://NewOSXBook.com/tools/supraudit.html
The usage mode is nearly identical to praudit - that is, supraudit can be used as the receiving end of a pipe (|) from an audit file, or run over one - commonly the supraudit are all uppercase, so as to not collide with those of its precursor. These switches allow for a variety of output formats or filters (as is shortly explained in "Usage Examples", below).
Unlike praudit(1), my tool - when operating on ioctl(2) codes, which allow it to set custom filters (or none at all) without affecting the local audit policy!. In simple words, you don't need to configure anything - just run supraudit directly on the pipe and see every BSD level operation! (Note, that Mach level operations cannot be audited, as the kernel does not support that).
Usage examples
The immediate and most useful feature is -S, which uses my own record format, rather than the default of Apple's. The format is very much like Linux's strace (and my own jtrace), and is super grep-friendly. You can toggle color (which really helps) using -C or the usual JCOLOR=1:
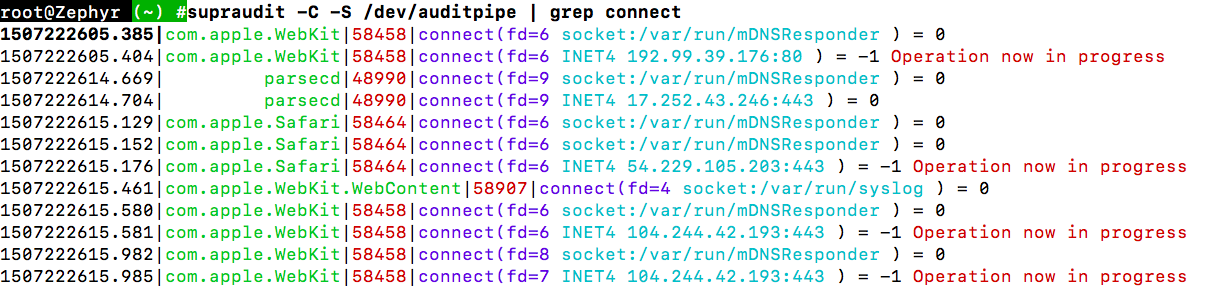
You can filter using grep and cut -d'|'.
grep are 'INET' (all network connections), 'INET4' (IPv4) and 'INET6'.
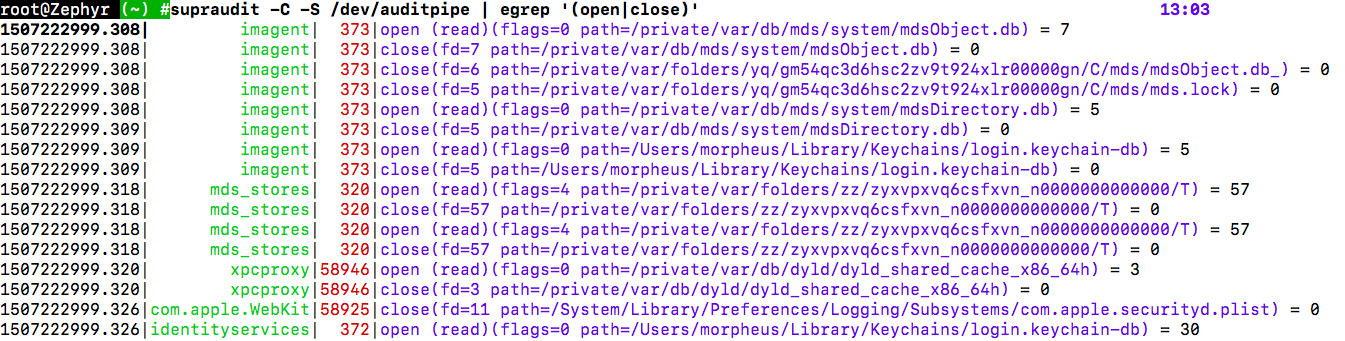
As another example, consider the equivalent of my filemon (sans reactive capabilities):
As a quick alternative to grep, you can use -F files, net or proc for builtin filters. This is recommended, since you can always apply grep(1) later. Also, doing so will automatically save an unfiltered audit log to
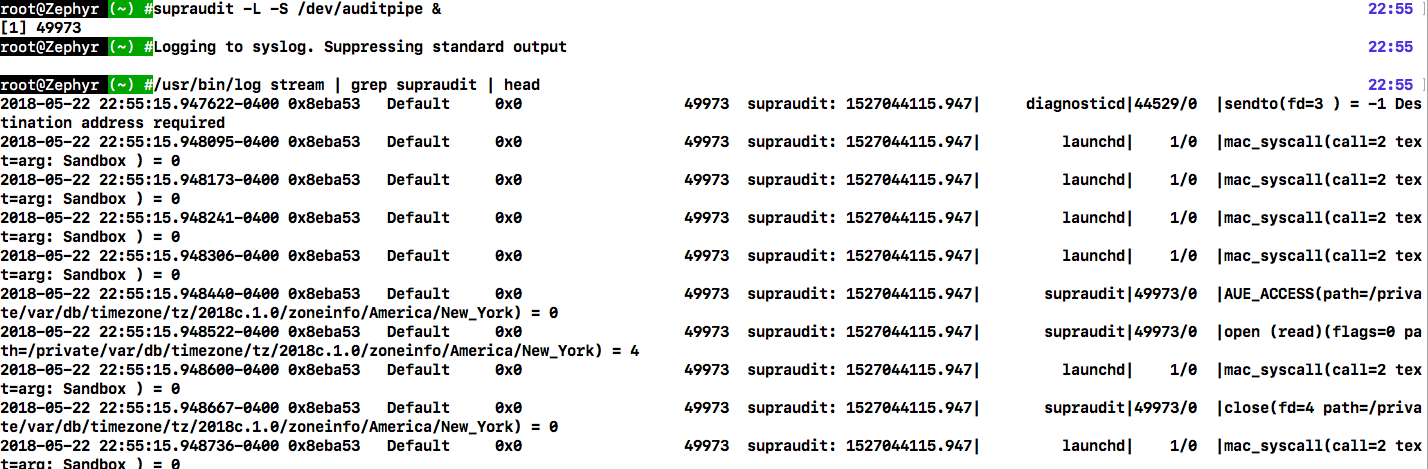
syslog/os_log integration
Using -L together with -S will log to local syslog/os_log:
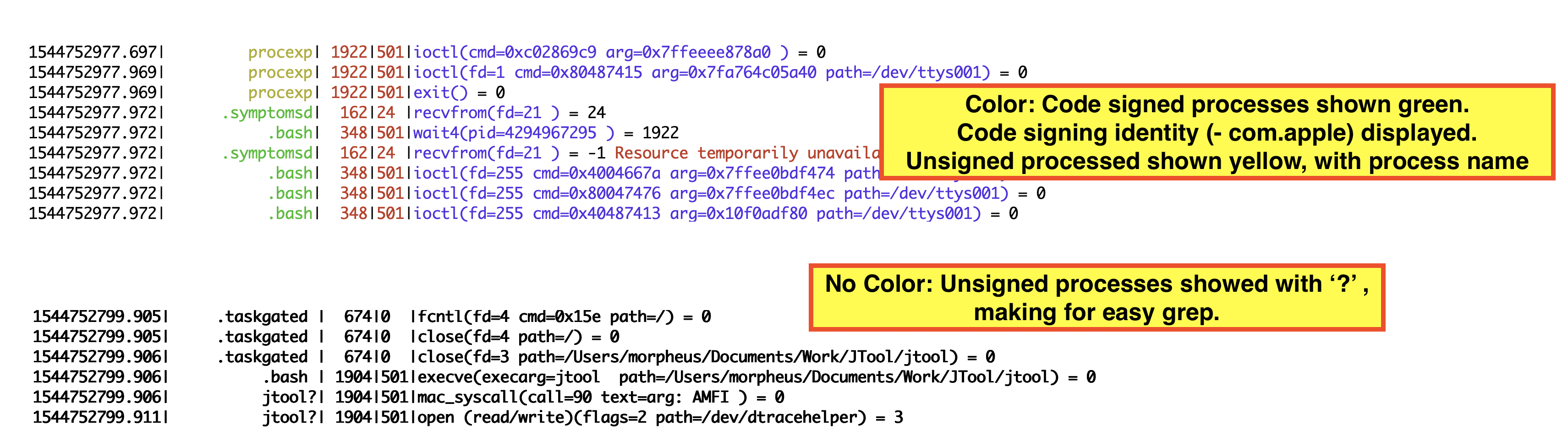
MacOS 14: Code signing support
Remote loghost
One of the audit mechanism's most glaring omissions is that, unlike syslogd, it doesn't do remote logging to a centralized server - which is imperative if you want to ensure log integrity, and vital if you have more than 5 machines, like in an enterprise. Well, that's been fixed. Using supraudit with -R will relay to a centralized server, but that requires...
Oh, yes.. There's Supraudit-PRO
A 'pro' version of Supraudit has even more features, including:
- Triggers: Using a config file you can have
suprauditexecute commands with basic variable substituion (e.g: 'on file access "/secret/*" kill subject'). This is not recommeded for security-sensitive prevention, becauase the audit mechanism is reactive. But it can be useful to set up a basic host intrusion mechanism. - Plugins: SUpraudit has a simple but powerful API for developers wishing to write their own programmatic plugins. This can be used to integrate with littlesnitch/bigbrother/twinsister/whatever.
- GUI (available soon): When you consolidate multiple audit logs, the data becomes crazy unmanageable. SUpraudit pro has a GUI which you can use to filter, sort, analyze, and even construct a timeline view showing you who-done-what.
The PRO version is in development, and will get a much more official and snazzier page when the fine folks at Technologeeks.com will get to it.
License
-
suprauditis FREE for personal use, and/or up to 5 hosts. - If you are going to use this in a commercial environment of 10+ hosts, you'll need to talk to products (a....t....) technologeeks ......com about licensing - and you probably want to get the PRO version anyway, which contains the server (for -R message relaying) and, soon the GUI.
- If you suggest an improvement or fix which I will incorporate, you get a free site license for life, and my thanks.
-
And now that you've read the license, feel free to get the binary (with its man page) here. The tar file also contains the reverse-and-forward engineed source of
praudit.
Examples
Changelog
supraudit its own webpage