Downloads
This page lists various tools which can be freely downloaded from this site. Note, the tools are binary - you will have to save them to a local file, then chmod +x to run them.
The usage is usually self-explanatory: Running a tool with no options or invalid ones will generate a usage message. The tools don't need root privileges (with the exception of Process Explorer, if you want to see all processes, or HFSleuth, when working with raw disk devices), so you can trust me and run them (or compile your own, where I provided the source)
The usage is usually self-explanatory: Running a tool with no options or invalid ones will generate a usage message. The tools don't need root privileges (with the exception of Process Explorer, if you want to see all processes, or HFSleuth, when working with raw disk devices), so you can trust me and run them (or compile your own, where I provided the source)
Quick Links:
Bonus downloads
These aren't found in the book, but as I continue my exploration of OS X and iOS, I'll add here:
- Supraudit - is a
praudit(8)clone on steroids which can track all activity on a MacOS system via the built-in BSM audit facility. It's every bit as good as filemon, and actually better, since it can do socket activity and process lifecycle as well. - Guesstalt - A
libMobileGestaltexample for iOS (only), accompanying this article. - procexp - Process Explorer - for Mac OS X and iOS! This tool attempts to A) replace Apple's terrible top(1) and B) provide as close a level of detail to Mark Russinovich's tool for Windows, though I'm still far off (working on it). This is a text mode, curses driven application (which makes it more useful than Activity Monitor, since it can be run over SSH). It's also runnable as a command line, to pipe for easily grep-able output. Constantly updated for new features I find in OS X 10.11 and iOS9. Includes WiFi signal strength indicator! You can move your iDevice or Mac around and ProcExp automatically shows and updates your connected SSID and RSSI)
Latest feature (10/02/15): Customizable display, Updated network statistics, power management
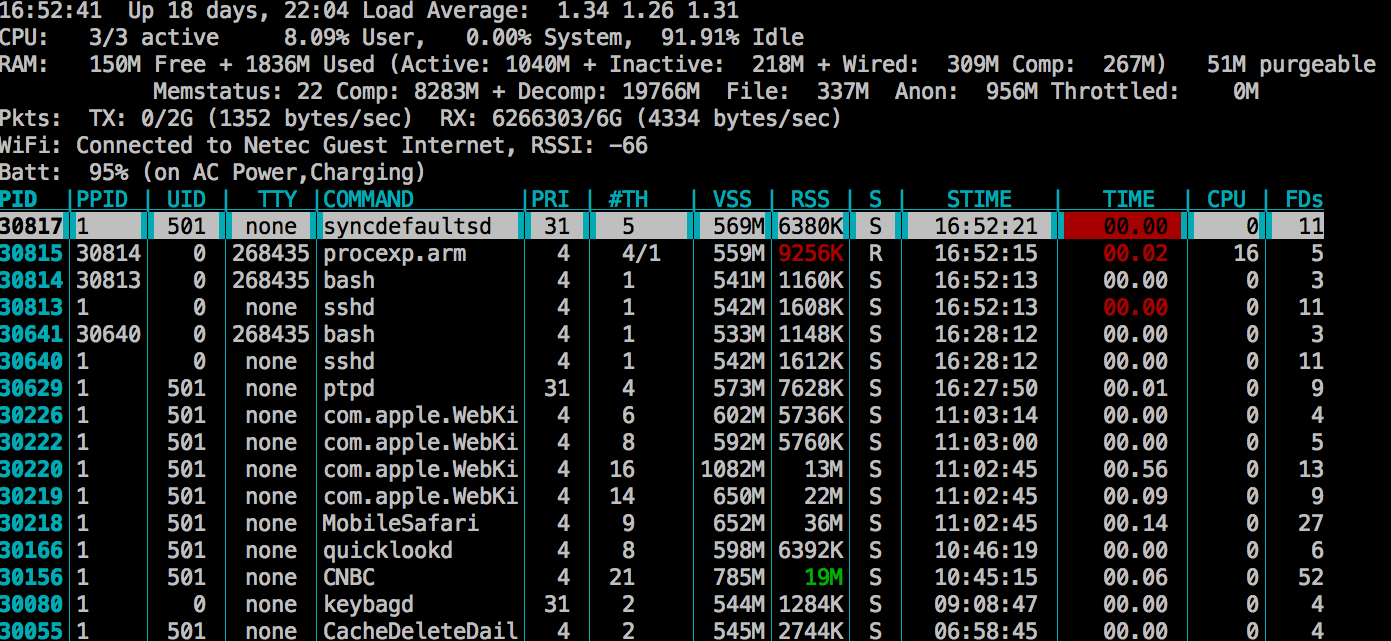
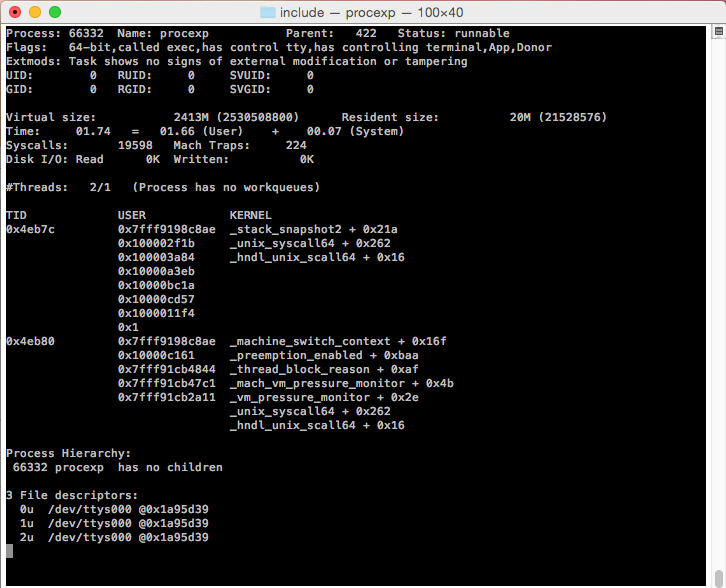
Process chart is fully navigable (with up-down arrow keys), sortable (with left-right and 'r' keys), configurale (with shift and left-right keys, or '-' to remove column), and hitting <enter> will provide more detail on each process.
- jurpleConsole - a clone of Apple's purple_console tool, used to connect from your Mac to services on the i-Device (jailbroken or not) via lockdownd using the private MobileDevice.framework. The service started on the device is syslog_relay (from /usr/libexec). Source code is here
Book extra content
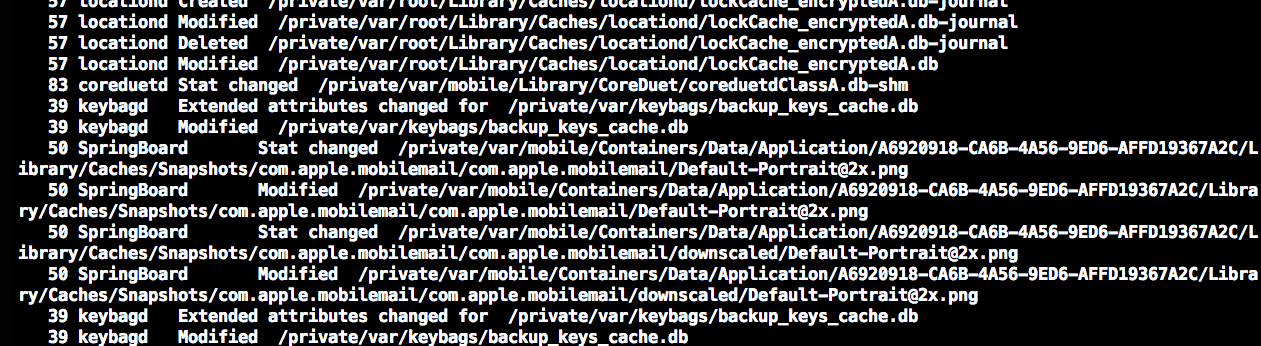
- Chapter 3: FileMon - a tool presented in Chapter 3, to demonstrate the functionality of the FSEvents formerly documented interface. Apple now wraps this with the FSEventStream abstraction, but if you want the low level C code, you now have the original in here, and a universal binary (with the updated source) in here. As simple as the tool is, it is just as invaluable, since you can peek behind the scenes what iOS Daemons are doing! It will look something like this:
- Chapter 4: JTool (Mach-O Analyzer)
jtool is a drop in replacement for
otool(1), nm(1), strings(1), andsegedit(1). It also has functionality not found in any of these tools, like a quick search for a binary string in file and memory simultaneously. The tool is undergoing constant revisions, and the latest one includes a custom disassembler with limited emulation functionality. Unlike otool and its Apple-supplied ilk, it won't break on "unknown load commands". Now also in a Linux ELF64 version.
For example, consider:morpheus@Ergo (~)$ ./jtool -d 0x800022ee ~/iOS/kernel.iOS6.iPod4,1
Processing /Users/morpheus/iOS/kernel.iOS6.iPod4,1:
800022ee f6444084 MOVW R0, 0x4c84 ; R0 = 0x4c84
800022f2 f2c00028 MOVT R0, 0x28 ; R0 = 0x284c84
800022f6 4478 ADD R0, PC (800022fa) ; R0=0x80286f7e "can't start backing store monitor thread"
;
; _panic(""can't start backing store monitor thread"");
;
800022f8 f015fc8a BL 0x15914 ; 0x80017c10 _panic
Pretty darn useful, especially now that iOS 6 uses PC-relative addresses and no longer has DCDs (which confuses IDA..). Also resolves symbols, and parses import tables, etc. Effectively replaces and extends Apple's own tools, including nm, dyldinfo, and pagestuff - all in one. - Chapter 5: Stack Snapshot
System call #365 is an undocumented, but really useful method to dump the stack backtraces of all threads in OS X and iOS, including kernel threads. OS X still contains
/usr/libexec/stackshot, though Apple has removed it from iOS. This tool, which is a beefed up version of listing 5-2 in the book, returns the stackshot functionality to iOS, and along the way demonstrates both how to call syscalls directly (using syscall) as well as some work with sysctl(2). I have provided the source code - Chapter 6: Imagine iOS images make heavy use of the IMG3 format. This tool can dump the various fields of a decrypted IMG3 file, and in particular can display the device tree files pertaining to various i-Devices. I have provided the source code for this
- Chapter 8: Joker
This tool (which shares some logic with the JTool) is custom designed for OS X and iOS kernels. It offers such features as automatically finding the Mach Trap Table and System Call Table (sysent) in the kernel - invaluable in the case of iOS, wherein these are hidden. You can also get an idea of
sysctl(2)MIBs exported by the kernel. The beta version also allows you to extract kexts from the kernelcache, as well as symbolify (by editing the Mach-O LC_[D]SYMTAB)morpheus@Erudite (~)$ ./joker ~/Documents/iOS/kernel.iOS6.0.1.iPod4 This is an ARM binary. Applying iOS kernel signatures Entry point is 0x80085084....This appears to be XNU 2107.2.34 Kern invalid should be 0x80028495. Ignoring those 10 _kernelrpc_mach_vm_allocate_trap 80014608 T 12 _kernelrpc_mach_vm_deallocate_trap 80014674 T 14 _kernelrpc_mach_vm_protect_trap 800146b8 T 17 _kernelrpc_mach_port_destroy_trap 8001475c T ... Suppressing enosys (0x801eb959) 1. exit 801d4a74 T 2. fork 801d7980 T 3. read 801eb584 T 4. write 801eb958 T 5. open 800b13a4 T 6. close 801ccab4 T 7. wait4 801d56bc T 9. link 800b18e8 T .. Kext: MAC Framework Pseudoextension (com.apple.kpi.dsep) Kext: Private Pseudoextension (com.apple.kpi.private) Kext: I/O Kit Pseudoextension (com.apple.kpi.iokit) Kext: Libkern Pseudoextension (com.apple.kpi.libkern) Kext: BSD Kernel Pseudoextension (com.apple.kpi.bsd) Kext: AppleFSCompressionTypeZlib (com.apple.AppleFSCompression.AppleFSCompressionTypeZlib) ..
Joker now has its own page - Chapter 12: vmmap(1) for iOS
This is a simple implementation of
vmmap(1)for iOS, based loosely on GDB'smacx_info_regions()function. I wrote this because (a) it's not included in any Cydia package I saw and (b) it's darn useful! Note, this will need the entitlements listed in chapter 3, since it relies ontask_for_pid(). This binary is also available in source form version, and forms the basis for the corerupt tool. - Chapter 16: HFSleuth Completely revised from the book, now as an interactive tool for OS X, iOS, and even Linux! (yep - on raw devices or DMG files only, though!). This tool enables you to explore the HFS+ B-Trees (attributes and catalog) interactively. Since I'm rewriting this (faced some iOS-related bugs which I have now resolved) I've been forced to square one, and still need to readd the cool functionality - such as fragmentation info, undelete, and low-level file access. So check this space often! Now supports DMG files, as well as pulling files from DMGs. Now comes with its own manual page. HFSleuth will not need root privileges when working on DMGs.
root@Erudite (/)# hfsleuth
HFSleuth> ?
dump Dump B-Tree node from current B-Tree
listfs List all mounted file systems and their types
fs Set active file system for operations to specific mount point or device
attributes Display the Attribute B-Tree details
catalog Display the Catalog B-Tree details
volinfo Display the volume header of the selected file system
snapshot Save a snapshot of the current B-Tree (catalog or attribute)
search Search for leaf by CNID
debug Toggle Debug traces on/off
verbose Toggle verbose mode on/off
xml Toggle XML Output on/off
pull copy file to /tmp (requires active file system)
dir list files (requires active file system) - synonymous with ls
cd Change directory (requires active file system)
ls list files (requires active file system) - synonmous with dir
help Display this help
? Display this help
! Shell command
quit Quit this program
HFSleuth> list
/ /dev/disk0s2 hfs 480D000 (volfs,local,rootfs,journaled,multilabel)
/Volumes/DeveloperDiskImage /dev/disk9 hfs 4209019 (nosuid,ro,volfs,local,nodev,multilabel,noowners,user-mounted)
Open a DMG, a local file system, or a device file
HFSleuth> fs /tmp/DMG/kernel_debug_kit_10.8.2_12c60.dmg
KOLY header found at 82285081:
UDIF version 4, Header Size: 512
Flags:1
Rsrc fork: None
Data fork: from 0, spanning 82215397 bytes
XML plist: from 82215397, spanning 69684 bytes (to 82285081)
Segment #: 0, Count: 0
Segment UUID: 00000000-00000000-00000000-00000000
Running Data fork offset 0
Sectors: 339009
Apple_HFS detected
Decompressing 294 blocks, Desc 1
338944 sectors - 173539328 bytes
Terminator
decompression done
RC was 0
HFSleuth(KernelDebugKit:/)> cat
catalog B-Tree dump:
Tree type: 0
Tree depth: 2
Root node: 3
First leaf: 37
Last leaf: 1
Leaf records 1086
Total nodes: 331
Free nodes: 289
Node size: 4096
Map node: 0
Compare: CF - Case Folding (case-insensitive)
#
#"ls" like emulation
#
HFSleuth(KernelDebugKit:/)> ls
folderthread 1KernelDebugKit
17 dr-xr-xr-x. 1 root wheel 1 Nov 1 19:56:35 2012 .HFS+ Private Directory Data
18 d-wx-wx-wx. 1 _unknown _unknown 1 Nov 1 19:56:35 2012 .Trashes
19 drwxr-xr-x. 1 root wheel 1 Aug 25 03:58:31 2012 AppleUSBAudio.kext
27 drwxr-xr-x. 1 root wheel 1 Aug 25 03:58:31 2012 AppleUSBAudio.kext.dSYM
34 -rwxr-xr-x. 1 root wheel 621 Feb 24 15:50:54 2011 createsymbolfiles
35 drwxr-xr-x. 1 root wheel 1 Nov 1 19:56:25 2012 DEBUG_Kernel
87 drwxr-xr-x. 1 root wheel 1 Aug 25 04:03:42 2012 IOATABlockStorage.kext
95 drwxr-xr-x. 1 root wheel 1 Aug 25 04:03:42 2012 IOATABlockStorage.kext.dSYM
....
#
#Pull files from a DMG to the host file system
#
HFSleuth(KernelDebugKit:/)> pull /mach_kernel 9975184 bytes written to /tmp/mach_kernel
- Chapter 17: lsock
Using the poorly documented
com.apple.network.statistics PF_SYSTEMprovider, you can get real time notifications of socket activity - much like Windows TCPView from SysInternals. This simple tool blocks until socket activity is registered, and displays it in anetstat(1)like manner.
Example: Output 17-3 from the book, running lsock on iOS (and catching apsd red-handed):
root@Podicum (/)# lsock -p tcp -a
TCP #1, IPv4, If 2, State 4, Pid: 10109 (sshd) 192.168.1.105:22->192.168.1.103:53784
TCP #2, IPv4, If 2, State 4, Pid: 81 (apsd) 192.168.1.105:50785->17.172.232.119:443
TCP #3, IPv4, If 1, State 1, Pid: 2 () 127.0.0.1:8021 (Listening)
TCP #4, IPv6, If 1, State 1, Pid: 2 () ::1:8021 (Listening)
TCP #5, IPv6, If 0, State 1, Pid: 2 () ::62078 (Listening)
TCP #6, IPv4, If 0, State 1, Pid: 2 () 0.0.0.0:62078 (Listening)
...
Since then, I've added a full screen (curses) interface and colors, making the tool a whole lot more useful: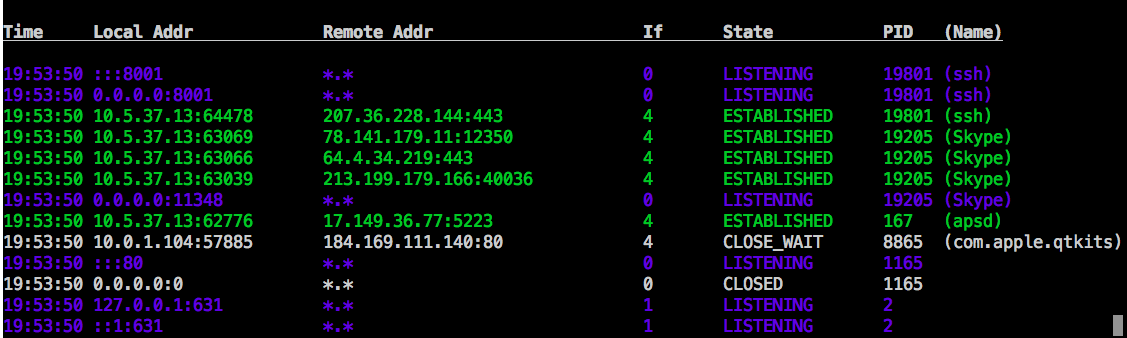
The binary supplied is a universal one (i.e. both Intel and ARM), but you can also get the source and compile it yourself. For full screen support on iOS, you will need to copy /usr/share/terminfo from OS X. - Chapter 18: JKextStat for iOS
This simple, but efficient
kextstat(8)replacement is the first tool to provide this much needed functionality on iOS. The tool can be used as the normal kextstat on OS X is, but can also output and XML dump, and (beta) a graph based view of all kernel extension dependencies. This binary is also available in source form version.